Claude API Key: Complete Setup, Security, and Troubleshooting Guide
Claude API Key: Complete Setup, Security, and Troubleshooting Guide#
One wrong header format can turn every Claude request into a 401 “Invalid API key” error in seconds. Most teams assume claude api key issues start at the model layer, but the real breakpoints usually happen earlier: key handling, auth headers, and missing guardrails for spend and rate limits. If you access Claude through Crazyrouter, the call path is straightforward: https://crazyrouter.com/v1/chat/completions, OpenAI-compatible SDK calls, and support for claude-3-opus, claude-3-sonnet, and claude-3-haiku. The platform also gives clear request caps you can plan around: 60 requests per minute on free tier and 600 on paid tier.
You will get a clean setup flow, from key creation to environment variable wiring, without hand-wavy steps. You will also get a security checklist that covers token limits, model scope, IP whitelist, and key rotation, so one leaked key does not drain your balance. Then we move into a repeatable troubleshooting path for 401, 403, 429, and 500 errors, plus cost controls based on token-level billing and usage tracking. Start with setup done right, and later debugging becomes faster and cheaper.
What a Claude API key is and why it matters#
A claude api key is a secret token your app sends with each API call. It proves request identity at the API layer, not at the human account layer. In a typical call, the key goes in the header as Authorization: Bearer YOUR_API_KEY, then hits POST /chat/completions on https://crazyrouter.com/v1.
Claude API key fundamentals#
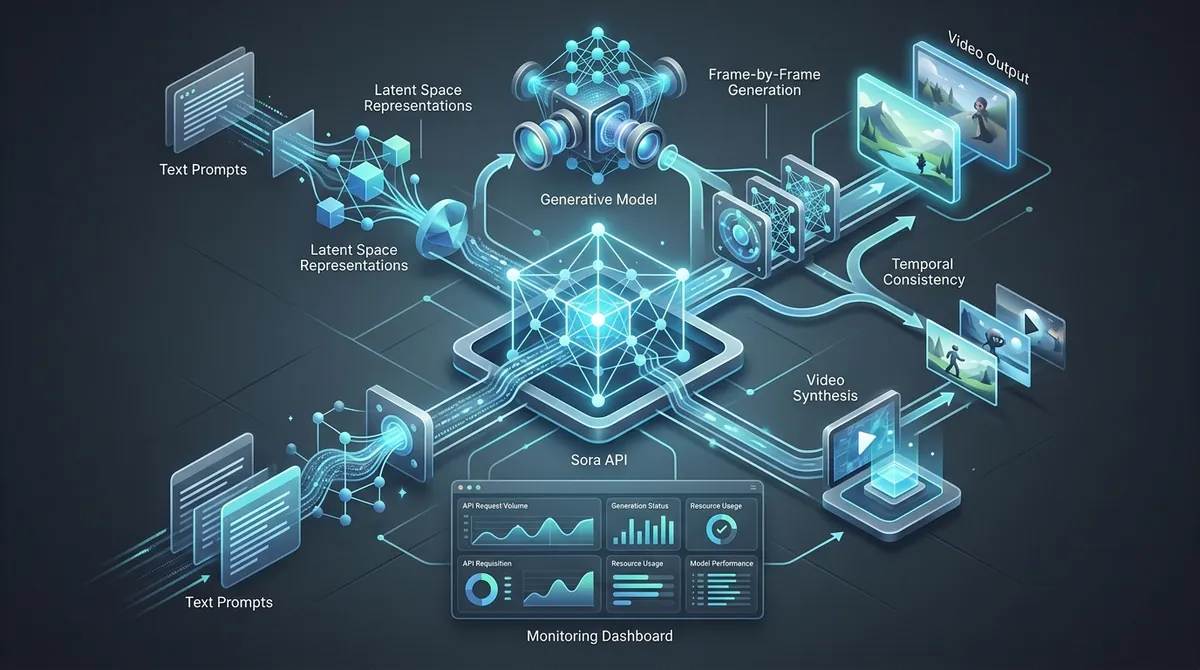
<!-- IMAGE: request flow showing app server -> Authorization Bearer key -> /v1/chat/completions -> Claude model response -->People often mix up API auth and normal login auth. They are not the same job.
| Access type | What it authenticates | Where used | Typical risk if exposed |
|---|---|---|---|
| API key | Server/app request identity | Backend request header | Unauthorized API spend |
| User login session | Human account session | Browser/app session cookie or token | Account takeover |
Source: Crazyrouter API and Authentication docs (Authorization: Bearer, /v1/chat/completions).
When to use a Claude API key (and when not to)#
Use a Claude key for backend services, scheduled jobs, internal tools, and server-side automations. That setup keeps secrets off user devices and lets you add controls like token quota, model allowlist, and IP whitelist.
Do not ship API keys in client-side JavaScript. Browser code is visible, so copied keys can burn balance fast. Use a backend proxy for web apps: browser calls your server, your server calls the model API. If you use Crazyrouter, you can keep one OpenAI-compatible server path and still call Claude models like claude-3-opus, claude-3-sonnet, and claude-3-haiku.
Before you generate your Claude API key: account, access, and billing prerequisites#
Create and verify your Claude key account#
Open your Anthropic account and complete email and phone checks right away. Most setup delays happen here, not in code. If your inbox filter catches verification mail, key creation stays locked until you confirm.
Use one login identity for all admin work. Mixing personal and work logins causes access confusion later, especially when you switch between browser profiles. Confirm account verification before you touch SDK code.
Set Claude key organization context and permissions#
A personal profile and a team workspace look similar, but key permissions can differ. In team setups, only users with admin-level rights can create or revoke keys.
| Workspace context | Who can create keys | Who should manage rotation |
|---|---|---|
| Personal account | Account owner | Same owner |
| Team workspace | Admin or owner (based on org policy) | Admin team |
Source: Anthropic console behavior and standard org permission practice; verify your org policy in settings.
If you cannot see API key controls, check your current workspace and role before opening a support ticket.
Prepare billing for Claude API key calls before launch#
Billing blocks a large share of failed first requests. Add a payment method, then set spend limits and alerts before production traffic starts. This protects you from runaway costs during testing loops.
Set a small cap for early testing, then raise it after stable logs. If you also test through Crazyrouter, you can use its free-tier cap of 60 requests/minute, then move to 600 requests/minute on paid tier as load grows.
<!-- IMAGE: Annotated screenshot of Anthropic console billing and usage settings relevant to API activation. -->How to get a Claude API key step by step (with first test call)#
If your goal is to call Claude models right now, use a claude api key from Crazyrouter and send an OpenAI-format request. You can keep one base URL, one key, and switch models like claude-3-sonnet without changing your SDK flow.
Generate your Claude API token in the console#
Go to https://crazyrouter.com and sign in.
Open Token Management at https://crazyrouter.com/token, then create a new token.
Set these fields while creating it:
- Name: use a clear label like
prod-claude-chatordev-test - Quota limit: cap spending for this token
- Expiry: set an end date for short-term keys
- Allowed models: allow only Claude models if this key is Claude-only
- IP whitelist: lock usage to your server IP if possible
Copy the key right away after creation. You only see it once in the UI. Store it in an environment variable, not in source code.
export OPENAI_API_KEY="sk-xxxxxxxx"
export OPENAI_BASE_URL="https://crazyrouter.com/v1"
<.-- IMAGE: Step-by-step UI sequence showing where to create a new Claude API key in the Crazyrouter token console, including name, quota, model scope, and copy action. -->
Test your Claude API key with cURL#
Run this minimal call:
curl https://crazyrouter.com/v1/chat/completions \
-H "Content-Type: application/json" \
-H "Authorization: Bearer $OPENAI_API_KEY" \
-d '{
"model": "claude-3-sonnet",
"messages": [
{"role": "user", "content": "Reply with: key works"}
],
"max_tokens": 20
}'
A valid response includes these top-level fields:
idobject(chat completion type)model(should matchclaude-3-sonnet)choices[0].message.content(the text output)usage.prompt_tokens,usage.completion_tokens,usage.total_tokens
Check model and usage every time. If the model name is wrong, your routing or request body is off. If usage is missing, treat that as an error path and retry with logs enabled.
If you hit a limit during testing, free tier is 60 requests per minute, paid tier is 600 requests per minute.
Quick start snippets for Claude key use in Python and JavaScript#
Use the OpenAI SDK format with Crazyrouter base URL.
import os
from openai import OpenAI
client = OpenAI(
api_key=os.getenv("OPENAI_API_KEY"),
base_url=os.getenv("OPENAI_BASE_URL", "https://crazyrouter.com/v1")
)
resp = client.chat.completions.create(
model="claude-3-sonnet",
messages=[{"role": "user", "content": "Ping"}],
max_tokens=30
)
print(resp.choices[0].message.content)
print(resp.usage)
import OpenAI from "openai";
const client = new OpenAI({
apiKey: process.env.OPENAI_API_KEY,
baseURL: process.env.OPENAI_BASE_URL || "https://crazyrouter.com/v1",
});
const resp = await client.chat.completions.create({
model: "claude-3-sonnet",
messages: [{ role: "user", content: "Ping" }],
max_tokens: 30,
});
console.log(resp.choices[0].message.content);
console.log(resp.usage);
If this call works, your key, endpoint, and model path are set correctly.
Claude API key security best practices for production#
A leaked claude api key is rarely a single bug. It is usually a chain: key in code, copied to logs, then shared in chat. Break the chain early. Treat every key as disposable. Set limits so one leak cannot drain your balance or expose every model.
Claude API key safe storage patterns that scale#
Use a secret manager for production. Plaintext files on servers or shared drives are easy to copy and hard to track.
Inject secrets through CI/CD environment variables, not hardcoded values. Keep variables masked in build logs. Your app should read keys at runtime from env vars.
For local work, keep .env files out of Git with .gitignore. Never commit sk-... keys. If you already did, remove the secret and rotate the key, since Git history keeps old commits.
When you create tokens in Crazyrouter, use per-environment tokens (dev, test, prod). Set token quota limits, model allowlists, optional expiry, and optional IP whitelist. If one token leaks, blast radius stays small.
Claude API key rotation and revocation playbook#
Rotate on a schedule every 3-6 months, and rotate right away after any suspected exposure. You should also rotate after staff changes or CI pipeline changes.
| Situation | Action | Downtime risk |
|---|---|---|
| Planned rotation | Create new token, deploy it, verify traffic, revoke old token | Low |
| Suspected leak | Revoke exposed token now, deploy backup token, audit logs | Medium |
| Confirmed abuse | Revoke all affected tokens, tighten model/IP/quota, reissue scoped tokens | Medium |
Source: Crazyrouter Authentication and API docs.
Zero-downtime sequence is simple: issue new token, deploy to all services, run health checks, then revoke old token after traffic is clean.
Claude API key leak vectors and prevention#
Common leak paths are Git history, app logs, screenshots, and team chat tools. Add pre-commit secret scanning to block pushes with sk- patterns. Redact auth headers in logs. Ban raw key sharing in tickets and chat.
Use least-privilege team access: only people who rotate or deploy keys should see them. Track token usage daily. Crazyrouter request caps (60 rpm free, 600 rpm paid) help you spot spikes fast.
<.-- IMAGE: Leak prevention checklist graphic covering code, logs, CI, and collaboration channels. -->
Manage costs and limits tied to your Claude API key#
A stable budget starts before production traffic. With a claude api key, you keep spend predictable when model routing, token caps, and monitoring work together. Treat these three settings as one control loop, not separate tasks.
<.-- IMAGE: dashboard view showing model usage split, token spend trend, and per-key quota status -->
Choose the right Claude API key model path for each workload#
Do not send every request to the same model. Route simple work to smaller models and reserve heavy reasoning for larger ones.
| Model | Good fit | Cost direction | Speed direction |
|---|---|---|---|
| claude-3-haiku | short replies, tagging, basic extraction | lower | faster |
| claude-3-sonnet | daily chat, coding help, mixed tasks | middle | middle |
| claude-3-opus | deep reasoning, hard analysis | higher | slower |
Source: Crazyrouter API model list (claude-3-opus, claude-3-sonnet, claude-3-haiku).
Control Claude API key token use in prompts and outputs#
If you only watch request count, you will miss the real cost driver: tokens. Crazyrouter billing is token-level, with separate input and output pricing. Keep prompts tight, trim old chat turns, and pass only context needed for the current answer.
Set output caps on purpose. Example: support replies can run with max_tokens around 200–400, then increase only for long-form tasks.
Implement Claude API key budgets, alerts, and retry limits#
You can use per-token quota limits in token management to stop runaway spend, then restrict model scope for each key. Add IP whitelist and expiry for production keys. Watch usage in the dashboard and set a monthly guardrail per environment key. Handle 429 with exponential backoff (for example 1s, 2s, 4s, then stop). Plan around Crazyrouter limits: 60 requests/min on free tier, 600 requests/min on paid tier.
Troubleshooting Claude API key errors quickly#
If your claude api key calls fail, map the HTTP status code to one root cause before touching code. Start with the status code, not guesswork.
Claude API key authentication and permissions errors#
Most fast fixes live in headers and token settings. Use this map:
| Error code | Common root cause | Fast fix | How to verify |
|---|---|---|---|
| 401 Unauthorized | Missing Authorization: Bearer ... header, bad key, wrong base URL | Send Authorization: Bearer YOUR_API_KEY and call https://crazyrouter.com/v1/chat/completions | Re-run with cURL and check error changes |
| 403 (insufficient_quota) | Account balance empty or token spending cap reached | Add balance or raise token limit in token settings | Dashboard usage and token limits page |
| 403 (model_not_allowed) | Token model scope blocks Claude model | Allow claude-3-opus, claude-3-sonnet, or claude-3-haiku for that token | Retry same request with updated token scope |
Wrong account context shows up after key rotation or deployment drift. Your app may still load an old secret from CI or container env.
Claude API key quota, billing, and rate-limit failures#
429 means request speed is too high for your tier: 60 requests/minute on free tier, 600 on paid tier. Add exponential backoff and a short queue. 500 means upstream or gateway trouble. Retry with delay, keep idempotent request logic, and log request IDs for support.
10-minute claude api key debug checklist for engineers#
- Reproduce with cURL using the same key, model, and payload.
- Validate
Authorizationheader,base_url, and model name. - Confirm deployment uses the newest key after rotation.
- Check token scope: model allowlist, quota cap, IP whitelist, expiry.
- Check dashboard logs for timestamp, status code, and request ID.
- If 429 repeats, lower burst rate and add jitter to retries.
<.-- IMAGE: Decision-tree diagram mapping Claude API key errors to immediate diagnostics and fixes. -->
Team workflows: secure sharing, access control, and operations#
Shared admin logins are where teams leak secrets. A safer pattern is simple: the owner creates tokens in Crazyrouter with quota caps, model limits, IP whitelist, and expiry; developers only receive environment variables, not the raw claude api key. Never share raw keys in chat or docs.
Claude API key governance for multi-person operations#
| Task | Owner | Developer | Approval flow |
|---|---|---|---|
| Create token | Yes | No | Ticket + reviewer sign-off |
| Rotate token | Yes | Trigger request | Change window + rollback note |
| Revoke on incident | Yes | Report issue | Immediate, then postmortem |
<.-- IMAGE: key lifecycle flow from request -> approval -> create -> deploy -> rotate -->
Practical claude api key tooling for team execution#
Tools like DICloak let you run isolated browser profiles for ops and dev work, so cloud console sessions do not cross and credentials are less likely to leak by copy-paste mistakes.
You can use DICloak teammate permissions to allow key rotation steps while blocking unrestricted admin actions in one shared browser environment.
Final production checklist and next steps#
Launch checklist for your claude api key#
- Store the key in a secret manager, not code or Git.
- Set token spend limits, allowed models, IP whitelist, and expiry in Token settings.
- Turn on billing alerts and test low-balance behavior.
- Validate retries for 429 and 500, plus clear handling for 401 and 403.
| Tier | Request cap |
|---|---|
| Free | 60 requests/min |
| Paid | 600 requests/min |
<.-- IMAGE: one-page go-live checklist with pass/fail boxes -->
Where to go deeper after claude api key rollout#
Read Anthropic model guides for prompt and context limits. Keep an internal runbook with sample errors, retry policy, and rollback steps.
Frequently Asked Questions#
How do I get a Claude API key if my account is new?#
Start by creating an Anthropic account and confirming your email. Next, make sure your account has API access enabled and complete billing setup, since key creation is usually blocked without a payment method. Then open the Anthropic Console, go to API Keys, and click Create Key. Give the key a clear name, such as staging-backend or prod-worker. Copy it right away and store it in a secret manager, not in plain text files.
Why is my Claude API key returning a 401 error?#
A 401 usually means authentication failed. First, confirm the claude api key is active and was copied correctly (no missing characters or extra spaces). Check your request headers: use x-api-key: YOUR_KEY and include a valid anthropic-version. Then verify your environment variable is loading in the running process, not just in your local shell. Finally, check whether the key was revoked or rotated, and update your deployment with the new secret.
Can I use a Claude API key in frontend JavaScript?#
Do not place a claude api key in browser code, mobile apps, or public repos. Anyone can open DevTools and steal it. Put your key on a secure backend instead. Your frontend should call your server, and your server should call the Anthropic API. Add rate limits, request validation, and logging on that backend route. This setup protects credentials and lets you block abuse quickly without shipping a new frontend build.
How often should I rotate a Claude API key?#
Set a fixed rotation schedule, such as every 60 or 90 days, and follow it across all environments. Rotate immediately after any possible leak, team offboarding, or security event. Keep overlap during rollout: create a new key, deploy it, verify traffic, then revoke the old one. Track owners and last-rotated dates in your runbook. This keeps downtime low and reduces the risk from stale credentials.
What affects Claude API key costs the most?#
Your bill is mainly driven by three things: model choice, token volume, and request count. Larger models usually cost more per token than smaller ones. Long prompts and long outputs raise usage fast, so trim system prompts and cap max output tokens when possible. Frequent calls also add up, especially in chat loops. Add caching for repeated prompts, batch background work when you can, and monitor token use per feature to catch spikes early.
How can teams share access without sharing one Claude API key everywhere?#
Use separate keys per service, environment, and team-owned workload. For example, keep one key for production API traffic and another for internal tools. Store each key in a secret manager (not Slack, docs, or .env files in repos). Restrict who can create or revoke keys with role-based admin access. Add a key naming rule, owner field, and rotation policy. This gives clear ownership, safer offboarding, and faster incident response.
Getting your Claude API key is only the first step; the key takeaway is that secure storage, least-privilege access, and regular rotation are what protect your integration over time. Start with a simple test request, verify your setup and error handling, then follow the official guidance as you build: Create your key, run a test request, and bookmark the official docs so your integration starts secure from day one.